Filter by
SubjectRequired
LanguageRequired
The language used throughout the course, in both instruction and assessments.
Learning ProductRequired
LevelRequired
DurationRequired
SkillsRequired
SubtitlesRequired
EducatorRequired
Results for "security policies"

University at Buffalo
Skills you'll gain: Model Based Systems Engineering, Systems Engineering, Product Lifecycle Management, Intrusion Detection and Prevention, Security Controls, Performance Measurement, Anomaly Detection, Machine Controls, Incident Response, Digital Transformation, Vulnerability Assessments, Software Development Life Cycle, Product Engineering, Cybersecurity, Supply Chain Management, Manufacturing Processes, Supply Chain Planning, Data Sharing, Manufacturing Operations, Constructive Feedback

Skills you'll gain: Cyber Security Assessment, Cybersecurity, Security Testing, Security Controls, Vulnerability Assessments, Incident Response, Intrusion Detection and Prevention, Malware Protection, Network Architecture
 Status: Free
Status: FreeThe University of Edinburgh
Skills you'll gain: Political Sciences, Liberal Arts, Social Studies, Psychology, Science and Research, Scientific Methods, Social Sciences, Research, Ethical Standards And Conduct, Public Policies

Google Cloud
Skills you'll gain: Kubernetes, Identity and Access Management, Cloud-Native Computing, Google Cloud Platform, CI/CD, Containerization, Application Deployment, Cloud Management, Scalability, Cloud Computing, Cloud Infrastructure, Load Balancing, Continuous Integration, DevOps, Continuous Delivery, YAML, Data Storage, Cloud Applications, Application Performance Management, Authorization (Computing)

LearnKartS
Skills you'll gain: Distributed Denial-Of-Service (DDoS) Attacks, Cloud Security, Penetration Testing, Cloud Computing, Cybersecurity, Mobile Security, Application Security, Cyber Threat Intelligence, Virtualization, Encryption, Cryptography, Vulnerability Assessments, SQL

University of Colorado System
Skills you'll gain: TCP/IP, Local Area Networks, Routing Protocols, Network Routing, Digital Communications, OSI Models, Network Protocols, Dynamic Host Configuration Protocol (DHCP), Network Security, Network Planning And Design, Network Architecture, General Networking, Network Performance Management, Computer Networking, Wireless Networks, Software-Defined Networking, Algorithms, System Programming, Data Integrity, Virtualization

Skills you'll gain: Endpoint Security, Application Security, Cloud Security, Cyber Attacks, Cybersecurity, Malware Protection, Information Systems Security, Security Awareness, Data Security, Cloud Computing, Network Security, Threat Detection, Encryption, Virtualization, Data Ethics

Skills you'll gain: Security Controls, Security Management, Information Systems Security, Information Assurance, Security Awareness, Data Ethics, Cyber Security Policies, Data Security, Information Privacy, Information Management, Change Control, Configuration Management
 Status: Free
Status: FreeCoursera Instructor Network
Skills you'll gain: Information Privacy, General Data Protection Regulation (GDPR), Personally Identifiable Information, Data Security, Data Governance, Data Ethics, Law, Regulation, and Compliance, Data Loss Prevention, Data Management, Security Controls, Regulatory Compliance, Compliance Management, Compliance Training, Data Sharing, Security Strategy, Regulatory Requirements, Data Processing, Risk Management, Employee Training, Risk Analysis
University of Colorado System
Skills you'll gain: Distributed Denial-Of-Service (DDoS) Attacks, Intrusion Detection and Prevention, Role-Based Access Control (RBAC), AWS Identity and Access Management (IAM), Amazon Web Services, Amazon Elastic Compute Cloud, Cloud Computing, Malware Protection, Cloud Infrastructure, Cloud Security, Load Balancing, User Accounts, Authorization (Computing), Network Security, Identity and Access Management, Threat Detection, Information Systems Security, Cybersecurity, Encryption, Geospatial Information and Technology

Skills you'll gain: Incident Response, Computer Security Incident Management, Intrusion Detection and Prevention, Threat Detection, Cyber Threat Hunting, Incident Management, Cybersecurity, Security Management, Security Information and Event Management (SIEM), Data Integrity

University of Pennsylvania
Skills you'll gain: Compliance Training, Compliance Management, Regulatory Compliance, General Data Protection Regulation (GDPR), Law, Regulation, and Compliance, Compliance Auditing, Information Privacy, Governance Risk Management and Compliance, Personally Identifiable Information, Regulatory Requirements, Communication Planning, Risk Management, Internal Communications, Procedure Development, Data Security, Continuous Monitoring, Business Ethics, Governance, Internal Controls, Risk Analysis
In summary, here are 10 of our most popular security policies courses
- Digital Manufacturing & Design Technology: University at Buffalo
- Cybersecurity Assessment: CompTIA Security+ & CYSA+: IBM
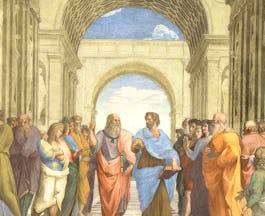
- Introduction to Philosophy: The University of Edinburgh
- Architecting with Google Kubernetes Engine: Google Cloud
- Advanced Cybersecurity: LearnKartS
- Computer Communications: University of Colorado System
- Systems and Application Security: ISC2
- Security Operations and Administration: ISC2
- Data Privacy and Protection Standards: Coursera Instructor Network
- Advanced System Security Design: University of Colorado System










